Table of Contents
ToggleWhat is a Tor browser? Surprisingly, if in this world there appeared a tool without using a VPN you can also freely surf the web anonymously. That is the Tor browser. So you already know what the Tor browser is? And how does a VPN work on it?
What is the Tor browser?
What is a Tor browser? Tor is a piece of software that helps to control web traffic through a system.
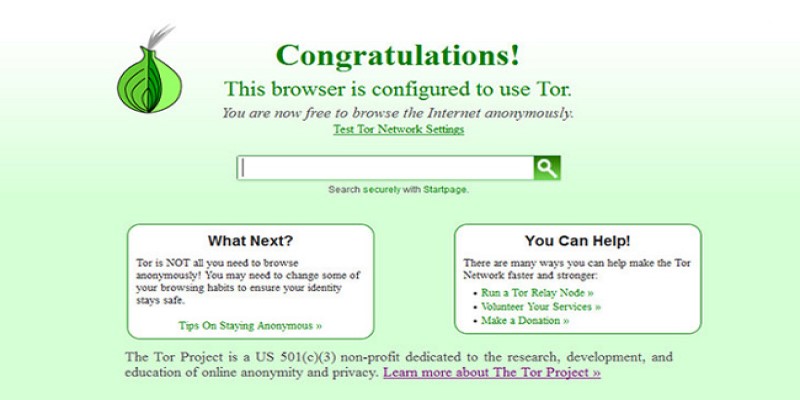
Tor Short for The Onion Router, Tor refers to the many layers of encryption used to protect the privacy of Internet users. Tor is a way to help you hide all of your online footprints, allowing you to access and disallow and download websites anonymously.
Hearing is beneficial, however, to work well Tor browser there is still VPN integration up there. What is a Tor browser? It was developed by a US Navy to ensure communication with the government. In Vietnam, many people know Tor Browser and call it roughly onion browser , sounds funny, right?
How to work on the Tor Browser
To be able to work on the Tor browser, you need to download and install Tor browser , all its activities are confidential, and there is no backup of the user’s activity log.

The way it works is to bundle your data into encrypted pre-loaded packets, wiping packages containing source information, as well as size, destination, and both Internet users’ time.
Those packets will be decrypted and encrypted in the strictest way, making Tor anonymous, and preventing you from being seen by others on the network.
How does Vpn work on it?
It is said that we do not need to use the Tor browser with VPN at the same time, however, this can help each other and ensure the security of Internet users.
Tor over VPN
In this case, if you connect to the VPN provider before connecting to Tor, the entry node will enter the VPN service provider’s IP address as the root of the data, then the Internet provider. will not know that you are connected to Tor, which helps you keep your internet history secure.
Another example is that using Tor over VPN can help protect against malicious node entries, helping to protect Internet users from reputable hackers. That’s why using a VPN with Tor is a must.
VPN over Tor
This method is done when you open the Tor browser and connect VPN to the Tor Network, followed by this stage connecting with the VPN provider through Tor.
The biggest advantage of this connection is that you can access websites that do not allow connections from known Tor exit nodes. This will help protect Internet users and help you avoid the unfortunate things that can happen while using the Internet.
However, this method may seem difficult to use when you have to reconfigure a VPN to use only through Tor, which makes Tor even more difficult to use.
Although they work differently, these two methods are always aimed at protecting the interests of Internet users, and if you are looking for a method of securing information in the Internet environment then, of course, you should consider these methods that we have shown above.
To learn more about the best VPN services to combine with Tor Browser, read the article Top 10 VPNs our global best of 2022